08 Mar File sharing is not what it used to be
File sharing is not what it used to be. In the beginning there was FTP, the File Transfer Protocol born way back in 1971 to move data through the Internet. It was the legendary port 21 of the TCP/IP connection where the server listened to our requests and then opened the data channel on which files traveled from one host to another.
Almost magic, zero security. But it gave us considerable powers: upload and download, management of remote file systems, resumption of interrupted transfers. So much so that FTP, a bit like radio, has never completely gone out of fashion. I still happen to use an FTP client from time to time, and when I do — not to mention when I FTP from the command line — it’s like going back to the early days’ thrill.
It may come as a surprise that it feels so sentimental to get back in touch with something technical as the fundamentals of networking. But after all, it’s nostalgia for a past that seems long gone. For most of us today, the internet has become invisible. A name, an idea.
In fact, after the GUI client freed users from the rigors of the command line — the first trade-off between power and ease of use — the progressive abstraction of the underlying network into what would slowly become “the cloud” began.
Two methods take off
The first service of this new genre that entered my daily life was MediaFire, born in 2005: it offered virtual storage, free in the basic version, where you could upload files directly via the web browser. At the time it gave me the impression of a real trailblazer. Its family included the famous RapidShare, since 2002, and an enormous offspring including the infamous giant Megaupload, with its Mega-brothers.
Alongside these forerunners of cloud storage, which were in continuity with FTP as they showed a folder system on a remote host, a second strand emerged: services that presented themselves as email extensions for large files, that could be a big problem for SMTP. Let’s not forget that way back when email was the main means of communication, finding it blocked by a heavy file attached carelessly was more than enough reason to quarrel.
One of the first I remember was YouSendIt, born in 2004: it let me upload files and enter email addresses through a web form, and at the end, it sent to the recipients a download link, with a security deadline. Any trace of the old FTP was expelled from the user experience since the actual data transfer operations remained hidden behind the scenes. No virtual space to manage, the user could only point to the only available goal: passing data to another user.
At the end of the day, this very well-defined and functionally constrained style proved to be a winner in the face of an immense population of consumers who crowded onto the network as well as around washing machines and lawnmowers. People who had no knowledge of computing and just needed to perform a conceptually simple task such as moving an object from one place to another. This is the approach adopted by WeTransfer, a company founded in 2009 that has now become the generalist file transfer antonomasia. “Send me a wetransfer” is now part of everyday language.
Real-world use cases have continued to hold up the separation between the two methods: specialized send-a-file services like WeTransfer vs. accessorized storage services like Dropbox, iCloud, Google Drive, etc. And this is despite the fact that the two areas increasingly tend to overlap in terms of functionality, with WeTransfer granting storage and cloud drives accompanying files from one user to another.
File sharing in the film industry
The distinction between the two methods is particularly visible in our industry: cloud-based media asset management (MAM) platforms. These are vertical applications dedicated to professional use in audiovisual production. A forefront on which gigantic masses of data are generated, up to hundreds of TB per single product, with traffic multiple of these figures. Rivers of data that must pass through the agile workflows typical of the creative industries, and be subjected to review and evaluation on the one hand, and to data processing on the other, by a wide variety of subjects belonging to many organizations. All with the highest degree of security.
The use cases on the two operational branches are well distinguishable. The action proper to the first branch is the viewing of streaming materials and involves mostly users with negligible computer skills. In the second branch, on the other hand, we find highly trained technicians working on high-resolution data, and here the main function of the platform is to move files from one processing stage to another.
Apart from the first act, which is always of course an upload to the cloud — either directly from the camera on the set, or from a hard disk in the lab — the subsequent processes somehow follow the division between the two lineages historically derived from FTP that we saw above. In fact, in MAM we find both, in the same platform or with delivery delegated to specialized third-party services, such as IBM’s Aspera or Signiant’s MediaShuttle. The latter, however, constitute additional IT systems to add to the stack, with the inevitable increase in security threats.
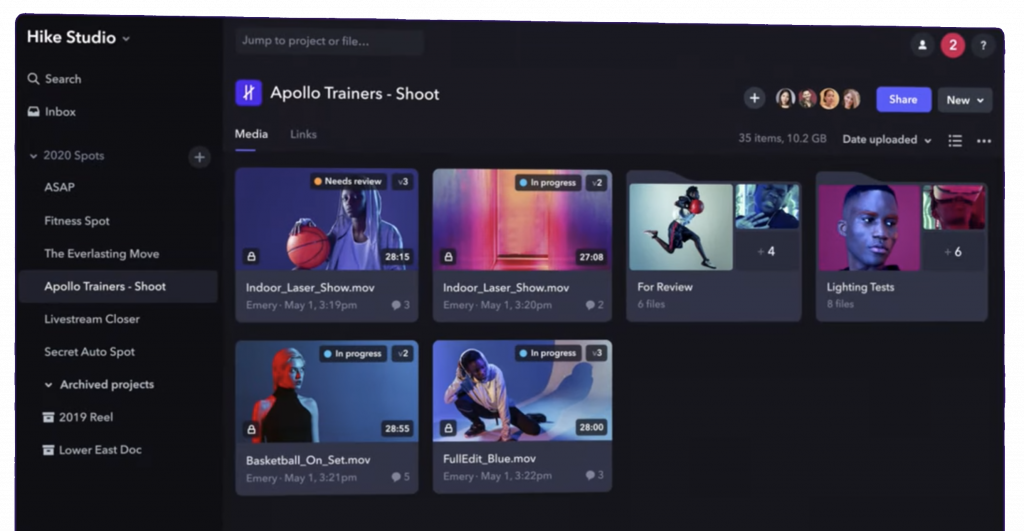
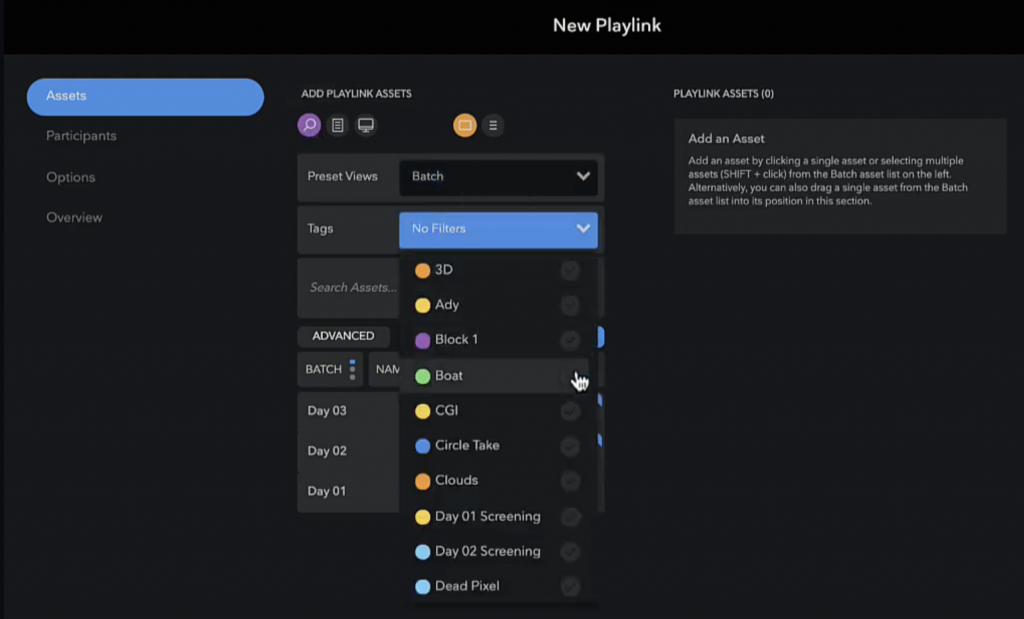
Normally, MAM for audiovisuals is therefore carried out on two tracks. First, data technicians upload and organize clips in folders, as in a classic remote file system, Mediafire-style. Then come views and downloads, and here the WeTransfer-style applies: sharing via links in the folders themselves or playlists prepared by the staff.
As good examples of the two methods we can respectively mention Frame.io’s folder sharing, and Moxion’s playlinks. All of these are links that open the door to the recipients of small reserved video worlds, mini-portals where you can find only the clips to watch and/or download, as an operator has prepared them.
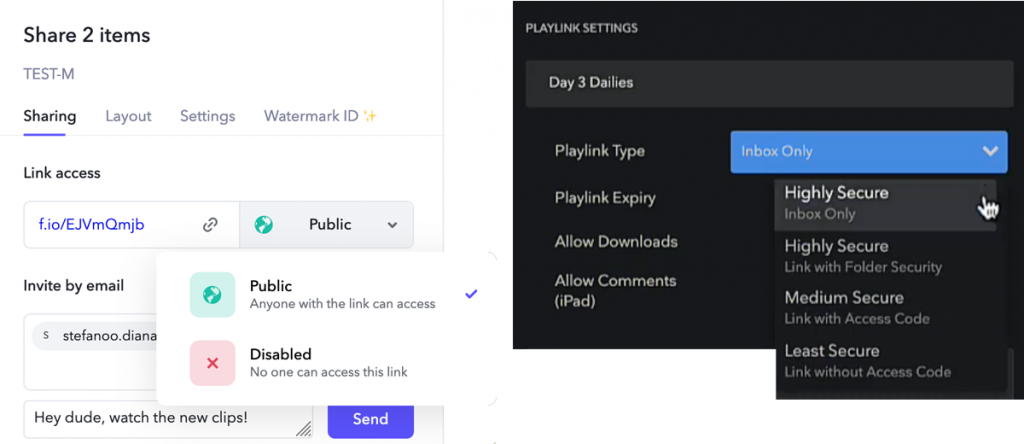
These links have a miraculous virtue: convenience. Just click the button in the email and you get your reward. Convenience, however, is the vestige of their consumer derivation. And we’re not in a consumer world at all here. The stakes are as high as the value of that data: pieces of new movies and TV series that will be marketed worldwide.
That’s why MAM’s platforms give you a choice of different levels of security, such as password protection, or login-only access. The relevant fact is that the link can also be sent in plain text via email.
We know from experience that this is a concession made to very insistent demand, that of many end-users who want the lowest possible, zero effort access threshold. Unfortunately, it’s a little deal with the devil that underestimates or tries to forget the dangers, the potential prices to be paid.
The mere existence of this possibility is a kind of invitation to the worst practices on the active side of security, where users do their own thing in defiance of the best technological defenses. Users who can’t wait to avoid precautions, for example by emailing the eventual password protecting the link together with the link, in the same message, not even encrypted. Bad practices well known to crackers of all kinds, who are always lurking behind the doors, ready to take advantage of it.
It should also be noted that the easy-link methods, whether to folders or playlists, relegate end-users to a passive position and involve a certain dependence on a priestly class of administrators, the only actors in the system who can prepare playlists and/or share folders, one-way.
There’s a different way
In Mnemonica, we have decided to leave these old methods behind and we have taken our own, different path.
First of all, we have abandoned the ancien régime of folders, with all the obsolete hierarchies they brought with them. Files are all our children, they are distinguished by the metadata they carry, tags thanks to which contents can be organized and searched in the most diverse and personal ways. Instead of folders, there are real screening rooms, made to bring people and media together, and people collaborate with one another through media. With an interface so simple that anyone can make their own playlists in a moment, without waiting for the gurus of the situation.
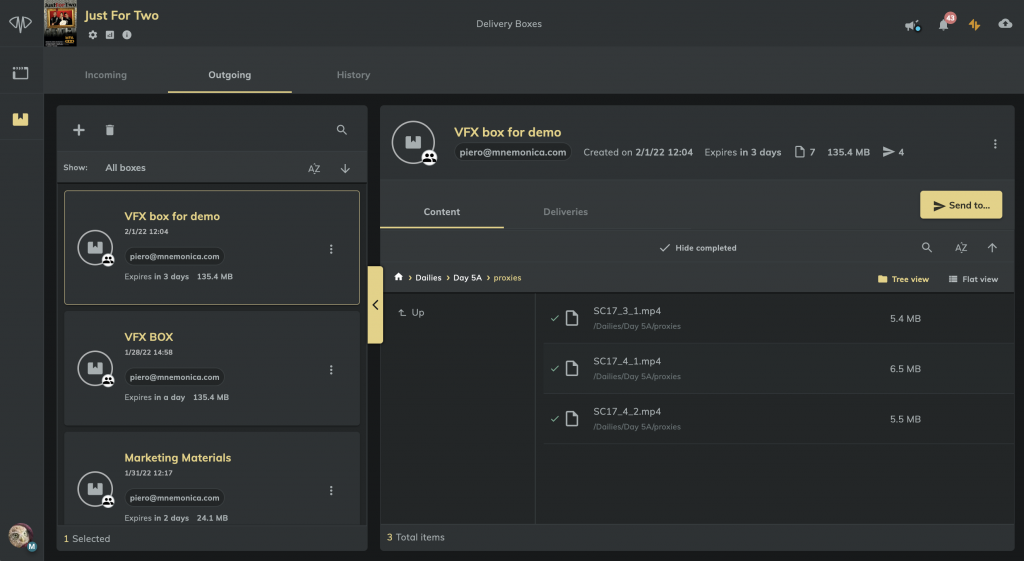
And most importantly instead of the WeTransfer method we have a complete two-way communication system between users of all roles. Not one-way paths from admins to periphery, with no return channel, but something that closely resembles email, with incoming and outgoing. The only difference is that our transport units are Delivery Boxes, containers that can accommodate sets of files and folders — yes, we accept others’ — as large and complex as desired.
The egalitarian conception of the Delivery Boxes makes life easy in several important use cases: for example, a post lab operator with the simple role of Guest will be able to exchange working files with his colleagues in the same project, in full autonomy. No time wasted asking for permission. Or worse, being intermediated by others with the result of downloading and re-uploading hundreds of GB several times.
In our view, independence is also a very good thing because it generates efficiency. But we did not forget the other keystone: security.
The possibility of sending links, encrypted or not, simply does not exist in Mnemonica. It is a thoughtful design, a choice we have reconfirmed with each release, resisting flattery, threats, and temptations. We have done this to help human beings not to fall into the tricks of convenience seen above. In film/tv productions they can translate into leaks and cost a lot of money. Delivery Box exchanges take place only between registered users, in the super-secure environment of Mnemonica.
Too tight? Not really, because we’ve done something nicer for our users: we’ve made our security as simple as possible, with the app acting as a master key. Almost magic, total security. This seems to us to be the best path on which technology can lead us.